Combatting Business Email Compromise: Strengthen Workflow to Protect Your Business
On June 18, 2025, Bobby Stewart, a product owner at e4, highlights the growing threat of Business Email Compromise (BEC) during a discussion on workflow vulnerabilities. With 38% of South African executives ranking BEC as a top cyber threat due to over seven million phishing attempts in 2023, organizations must assess email security processes, particularly in high-value transactions, to protect against fraud.
Identifying Workflow Vulnerabilities in High-Value Transactions
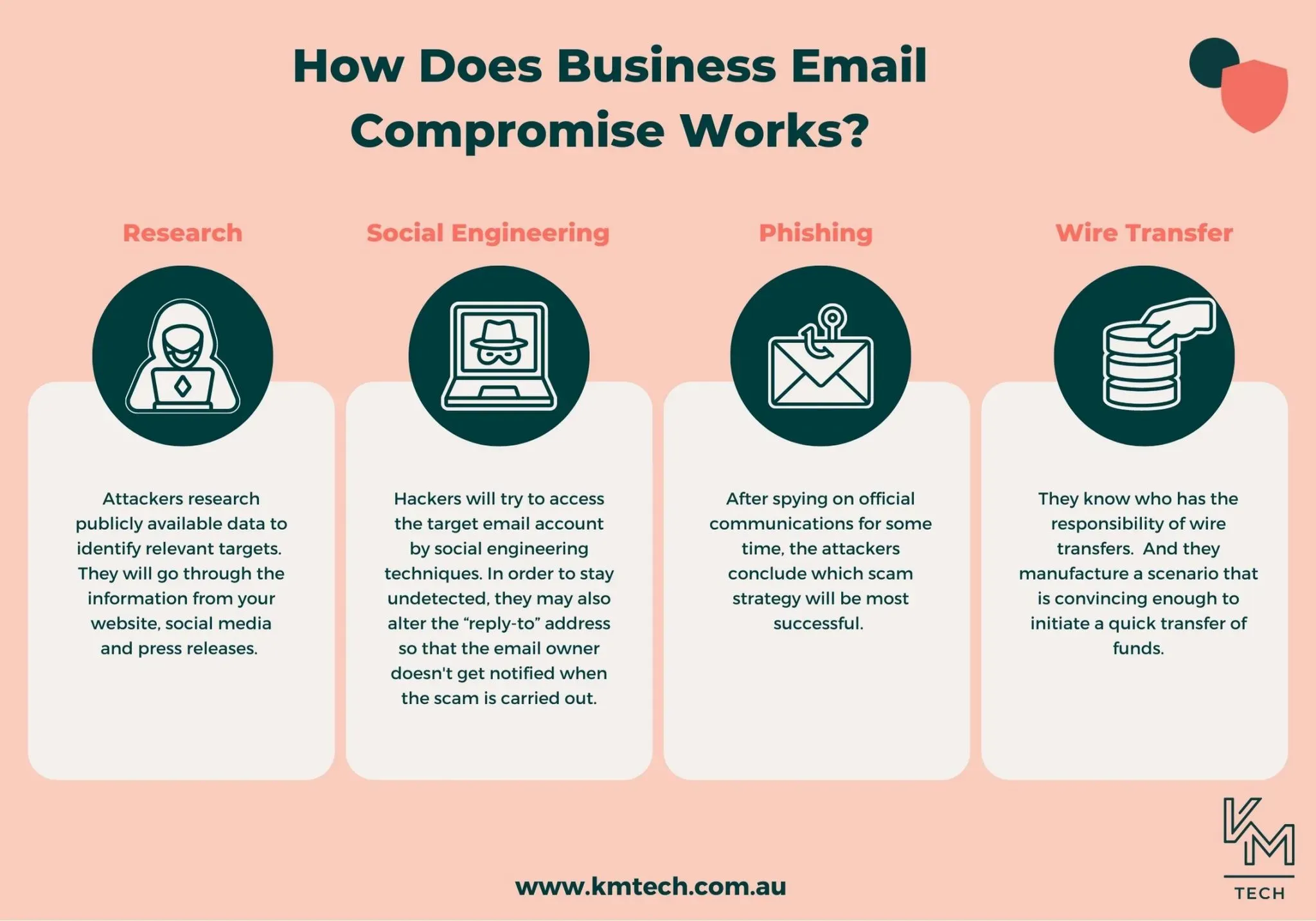
Business Email Compromise (BEC) exploits vulnerabilities in email-dependent workflows, notably in high-value transactions where identity verification often remains inadequate. Bobby Stewart states, “BEC exploits weaknesses in workflow.”
A notable incident involved a homeowner mistakenly signing bond-cancellation documents due to unverified communications. Stewart noted, “Such an attack occurs not because of firewalls or strong passwords.”
Traditional security measures cannot fully protect organizations; they’ll only succeed if integrated into transaction workflows. As Stewart emphasized, “most BEC vulnerabilities are mitigated” when safeguards are constructed into communication methods.
Effective collaboration between multiple parties in significant transactions remains a critical challenge. Security protocols must encompass every stakeholder to minimize exposure to BEC.
Best Practices to Mitigate Business Email Compromise Risks
Creating a secure, authenticated environment for all parties involved is an essential strategy in mitigating BEC risks. Stewart underscores that secure communication allows entities to transfer sensitive information away from unprotected channels.
Integrating end-to-end encryption offers a layer of protection, safeguarding document sharing among participants in high-value transactions. This minimizes the risk of impersonation and fraudulent activities, according to Stewart.
Organizations must reevaluate their communication processes, diagram each transaction step, and redesign workflows. Stewart suggests identifying steps still relying on unprotected methods to bolster defenses against BEC.
In conclusion, as Business Email Compromise continues to pose significant threats to organizations, especially in high-stakes transactions, it is imperative that businesses adopt a proactive approach to mitigate vulnerabilities. By embedding secure, authenticated processes and re-evaluating communication workflows, companies can transform potential weaknesses into resilient defenses against cyber fraud.
Let us know your thoughts by leaving a comment below!
Don’t forget to share this article with others who may find it helpful.







